Hostile actors are already harvesting encrypted data today to decrypt it tomorrow with quantum computers. How can sensitive information be protected?
🛡️ The strategy rewriting the rules of cybersecurity
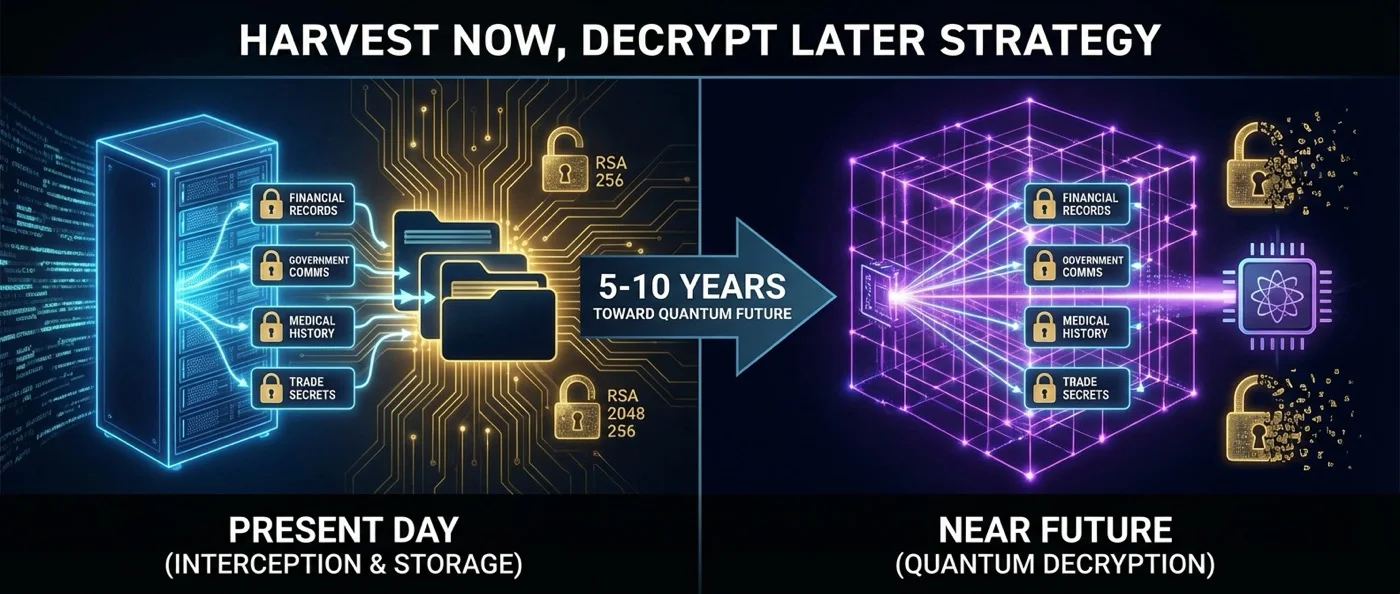
In July 2022, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued an unusual warning: it urged organizations to immediately begin transitioning to cryptographic standards resistant to quantum computers. The reason was not some sudden breakthrough — it was the acknowledgment of a threat already in motion: the "Harvest Now, Decrypt Later" (HNDL) strategy.
The idea is simple yet alarming. Hostile state and non-state actors intercept and store encrypted data today — diplomatic communications, medical records, military plans, banking transactions — with the intent to decrypt them in the future, once they gain access to sufficiently powerful quantum computers. That date is called "Q-Day" or “Y2Q,” in analogy with the notorious Y2K problem.
🔓 Why today’s cryptography is vulnerable
The vast majority of modern public-key encryption systems rely on three mathematical problems: integer factorization (RSA), the discrete logarithm problem (Diffie-Hellman), and the elliptic-curve discrete logarithm problem (ECC). For classical computers, these problems remain computationally infeasible at large key sizes.
In 1994, mathematician Peter Shor at Bell Labs presented a quantum algorithm that solves all three problems in polynomial time. Shor's algorithm exploits quantum superposition and the quantum Fourier transform to find the period of a function — and through it the prime factors of a number. An RSA-2048-bit key, which would take billions of years on a classical supercomputer, could theoretically be broken in less than 8 hours by a quantum computer with roughly 20 million “noisy” qubits, according to an estimate by Gidney and Ekerå (2021).
Today, the largest quantum processors have a few hundred or thousand qubits — far too few to run Shor's algorithm on practically large keys. But the question is not whether we will get there — it is when.
⏳ The timing paradox: why we must act now
Here lies the real danger of HNDL. Data intercepted today may remain sensitive for decades: medical records, national secrets, strategic business plans, biometric data. According to Mosca's theorem, if the sensitivity lifetime of data x plus the migration time to new cryptographic standards y exceeds the time until Q-Day z (i.e., x + y > z), then the organization is already exposed.
A 2025 report from the German Federal Office for Information Security (BSI) estimates that the transition to post-quantum standards may take 5–15 years for large organizations. This means that even if Q-Day is a decade away, time to act is already running out.
In August 2023, CISA, the NSA, and NIST published a joint factsheet titled "Quantum Readiness," emphasizing that HNDL attacks constitute a real and ongoing threat, not a hypothetical future scenario. A 2022 survey showed that 50% of organizations are already worried about this exact scenario.
📜 The new standards: NIST’s post-quantum cryptography
In August 2024, NIST (the National Institute of Standards and Technology) published the first three finalized post-quantum cryptography standards — the result of a standardization process that began in 2016:
- FIPS 203 — ML-KEM (CRYSTALS-Kyber): A key encapsulation mechanism based on lattices. It uses the Module Learning with Errors problem, believed to be resistant to both classical and quantum attacks.
- FIPS 204 — ML-DSA (CRYSTALS-Dilithium): A digital signature scheme also based on lattices. It protects the authenticity of communications.
- FIPS 205 — SLH-DSA (SPHINCS+): A digital signature scheme based on hash functions — an entirely different mathematical approach that provides alternative security.
In March 2025, NIST also announced the fifth algorithm, HQC (code-based), as a backup alternative. The logic behind using multiple mathematical families is clear: if a vulnerability is discovered in one category (such as lattices), the others continue to provide protection.
🏢 Who is already deploying post-quantum protection
The first major technology companies have begun the transition. In February 2024, Apple announced the PQ3 protocol for iMessage — a hybrid system combining classical cryptography with post-quantum algorithms and supporting continuous key rekeying. Apple stated that PQ3 “surpasses the protections of all other widely deployed messaging apps.”
Signal introduced the PQXDH (Post-Quantum Extended Diffie-Hellman) protocol in September 2023, integrating post-quantum key exchange. Google is already using hybrid cryptography in TLS tests and presented a post-quantum FIDO2 security key in collaboration with ETH Zürich in August 2023.
The strategy of “hybrid cryptography” — combining classical and post-quantum algorithms — represents today's best practice. If a new post-quantum algorithm proves vulnerable to classical attacks (as happened with SIDH/SIKE which was “broken” in 2022), the classical layer continues to protect the data.
🔗 Beyond algorithms: physical transmission security
A complementary approach targets the “harvest” component of the HNDL threat directly. Physical Layer Security methods modify the optical signal itself in fiber-optic networks, “burying” it within noise, making it impossible even to intercept the encrypted signal. If the attacker cannot intercept the data, there is nothing left for future decryption.
Companies such as CyberRidge have begun providing commercial “harvest-proof” optical encryption solutions, with field trials achieving 100 Gbps throughput on existing fiber-optic networks. This “defense in depth” — interception prevention plus post-quantum cryptography — may be the most complete answer to the HNDL threat.
🚀 What this means for the future
The “Harvest Now, Decrypt Later” strategy represents a rare case in cybersecurity: a threat that demands action before it fully materializes. The transition to post-quantum cryptography is not a matter of technical curiosity — it is a matter of national security, economic stability, and personal privacy.
The European Union published a coordinated PQC transition roadmap in June 2025. The Dutch intelligence services (AIVD) released a detailed PQC Migration Handbook in December 2024. Even the U.S. Federal Reserve is investigating the implications of HNDL for distributed ledger networks.
Encrypted data being transmitted right now is not only protected against today's computers — it must withstand tomorrow's as well. The race between data harvesting and the development of post-quantum cryptography has already begun — and its first results will determine the security of information being exchanged today.